5 Reasons that your Business is at Serious Risk
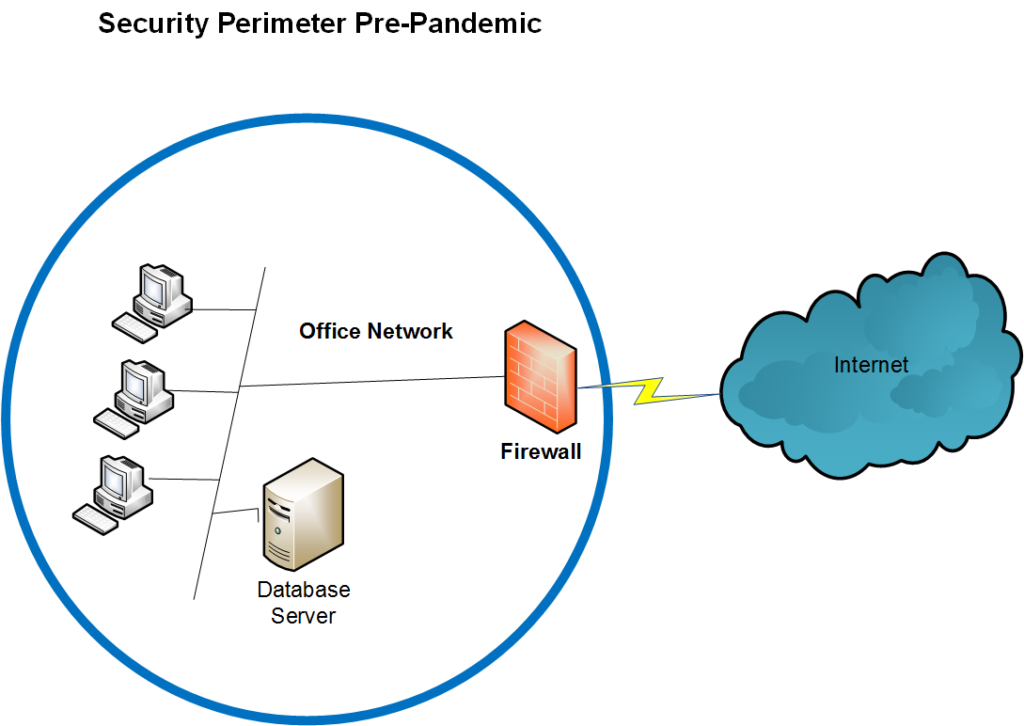
What you may have inside your Businesses Here are just a few of the situations IT Security Solutions has encountered when performing an assessment. All of the comments are focused on organizations with more than 2 computers in their network, a Firewall and Virus protection on each computer. If this describes your organization, then your […]
