Cybersecurity for SMBs: Protecting the Backbone of America

In this engaging `cybersecurity podcast`, we hear from `cybersecurity expert` Chase Cunningham as he introduces guests Maggie Dillon and Albert Whale, focusing on individuals who actively contribute to their field. This discussion provides valuable insights for `cybersecurity for entrepreneurs`, emphasizing `business protection` through proactive strategies. The conversation highlights the importance of a strong `founder mindset` […]
Cyber Chomps Episode #5 – Albert E. Whale, Maggie Dillon, and Alan Elliott, #Hacked2

Cyber Chomps Episode #5 Albert E. Whale, Maggie Dillon, and Alan Elliott, #Hacked2 Thank you and shout out to Joshua Bruyning for having us on the 5th episode of his podcast Cyber Chomps! Check out the latest from our #Hacked team, including Albert E. Whale, CEH CHS CISA CISSP BSEE CMMC-RP and Alan Elliott! Protecting your Data (both business and personal) […]
Interview with Security Researcher (one of the Co-Authors) #HACKED2

I was honored to be interviewed by the Security Researcher. He has a definite way with words, and we had a great conversation. Here’s some extra information from his channel. Security Researcher: I have been working on some things for you. Real things that will help you better protect yourself from modern day cyber threats. […]
Medallion XLN Podcast Ep. 8

Cybersecurity is a field in computer science that is overlooked until it is too late. Albert E. Whale is an expert in the field of Cybersecurity and in Episode 8 of the Medallion XLN podcast we talk about his book #Hacked as well as his crowdfunding effort for ITS-SAFE as well as expert takes on how to […]
The Cyber Field Podcast

[vc_row][vc_column][vc_column_text] I was honored to be a guest speaker on The Cyber Field podcast with Tom Albert. We discussed the importance of developing a cybersecurity strategy and how to keep your business safe from cyber attacks. I shared my tips for protecting your company’s data, and we also talked about the unseen attacks. It was […]
Cybersecurity – Do You Think You’re Really That Secure?
NEW PODCAST EPISODE Cybersecurity – Do You Think You’re Really That Secure? In this episode, Jennifer talks with Albert Whale from IT Security Solutions about cybersecurity and Albert shares some really scary information about security and how we may feel we’re safe but the hackers are out there watching and waiting for us to do […]
SWAT Assessment for Cybersecurity
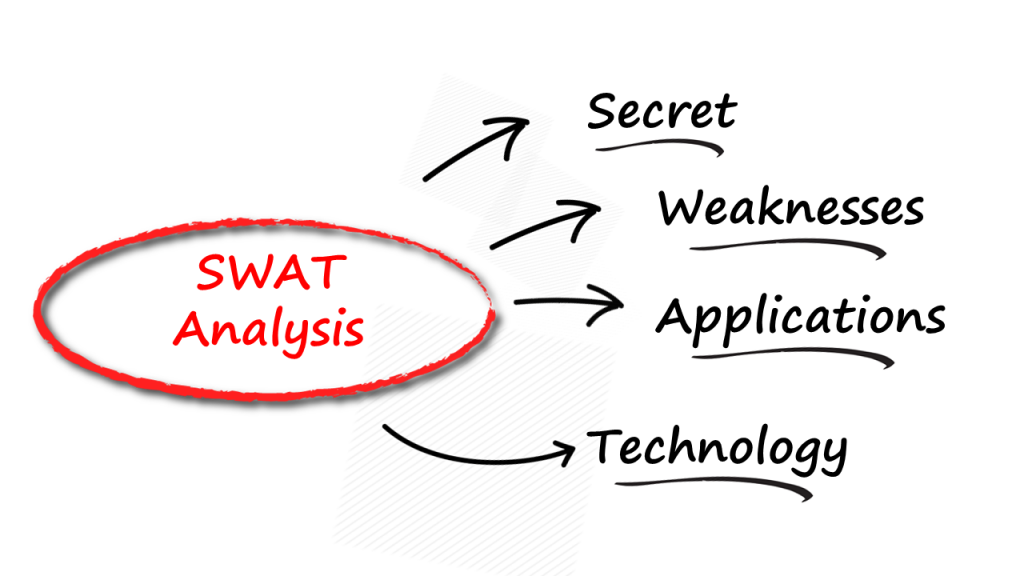
SWAT Assessment for Cybersecurity by Albert E. Whale, CEH CHS CISA CISSPFounder & CEO Attacks are running full speed ahead Everyday new attacks are reported in organizations of various sizes. Some of the attacks are recent, most are attacks that occurred months earlier, and are just recently being discovered. What makes these events so difficult […]
Ransomware is costing Millions of dollars per day.
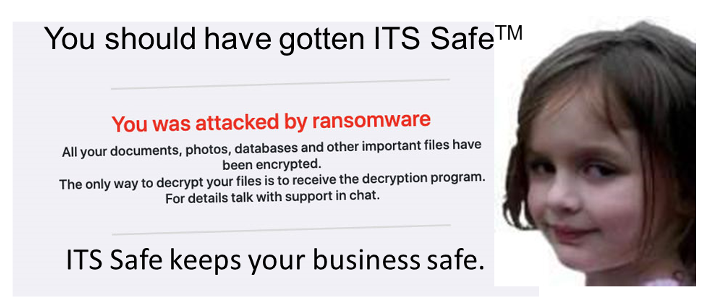
Ransomware is costing Millions of dollars per day. Written by Albert E. Whale, CEH CHS CISA CISSP BSEEMay 9, 2021 Ransomware is costing Millions of dollars per day. Maybe you think that I’m exaggerating, I’m not. The cost in the Healthcare industry alone in 2020 was over $21 Billion, that’s only in Healthcare. What happens to […]
5 Reasons that your Business is at Serious Risk
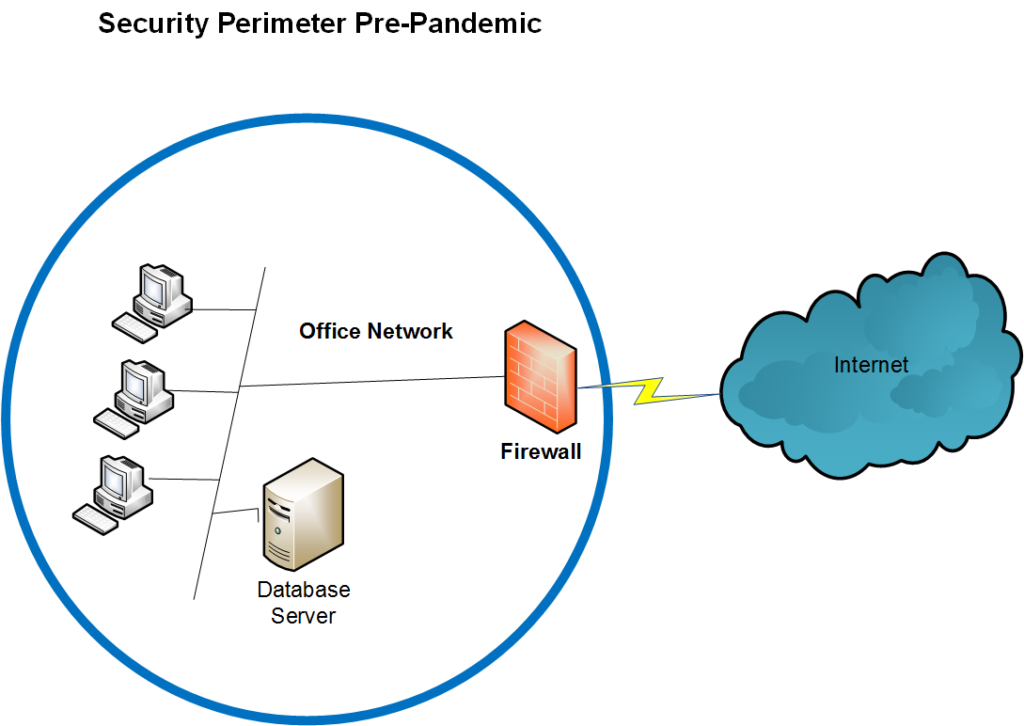
What you may have inside your Businesses Here are just a few of the situations IT Security Solutions has encountered when performing an assessment. All of the comments are focused on organizations with more than 2 computers in their network, a Firewall and Virus protection on each computer. If this describes your organization, then your […]
Its time for a Paradigm Shift for cybersecurity
ITS Safe™ Security Appliance Seeing the Unseen A shift in the security paradigm needs to address the Unseen attacks in the environment. Detecting the Unseen activities in the environment explains why there are so many attacks being reported on a daily basis. The unseen attacks depend on the ability of the attackers to hide in […]
